binwalk
A firmware analysis tool for identifying and extracting files embedded inside binary images.
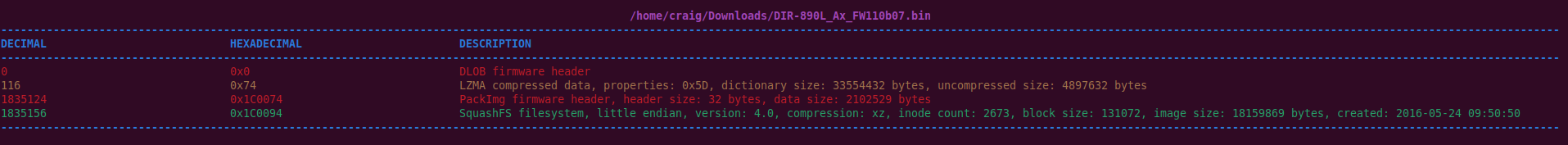
binwalk scans binary files to identify and optionally extract embedded data — file systems, compressed archives, kernels, and other payloads that have been packed into a single firmware image. Originally written in Python, v3 was rewritten in Rust for speed and accuracy.
Features
- Signature scanning across a wide range of file and data types
- Automatic extraction of identified components
- Entropy analysis to detect unknown compression or encryption
- Recursive extraction to unpack nested archives
- Support for common firmware formats (SquashFS, JFFS2, LZMA, gzip, and more)
- Integrates as a Rust library for custom tooling
Basic usage
# Scan a firmware image for embedded files.
binwalk firmware.bin
# Extract all identified files.
binwalk --extract firmware.bin
# Show entropy graph to detect encrypted regions.
binwalk --entropy firmware.bin
Availability
Available on Linux and macOS.